-
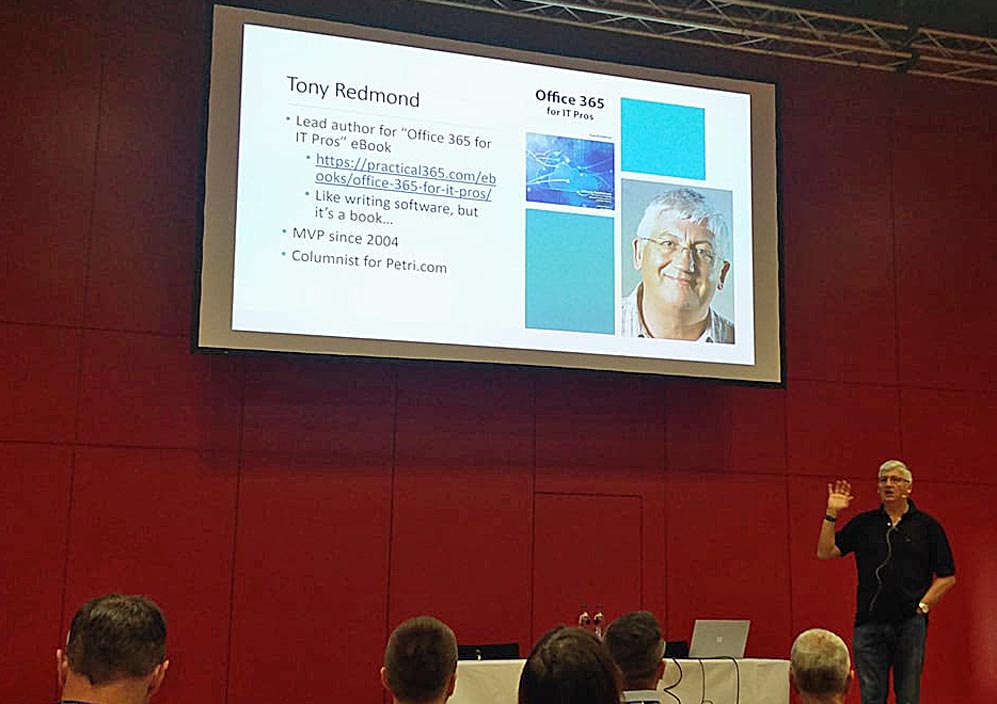
European Collaboration Summit 2018
Experiences from the European Collaboration Summit 2018, held in Mainz, Germany, May 28-30 2018.
-

Galapagos Photo Experiences
We recently visited the Galapagos islands. This blog post is a collection of photos from the trip, where I proved to fail to get anywhere close to capturing the Big 15 of Galapagos species.
-
Office 365 Exposed, Episode 11
Last week, I chatted with MVPs Paul Robichaux, Alan Byrne, and Vasil Michev in the palatial surroundings of the Continental Hotel in Budapest, and Paul taped the conversation as episode #11 in our “Office 365 Exposed” series. You can listen to the recording on Paul’s website or iTunes (sometimes it takes…
-
New Office 365 book from Microsoft Press
Despite what people might think, I welcome the release of the new edition of “Microsoft Office 365 Administration Inside Out.” There is nothing like competition to drive an increase in standards, and even though I think the Office 365 for IT Pros eBook (also available from Amazon Kindle) is pretty…
-
Announcing Office 365 for IT Pros Fourth Edition
The writing team is thrilled to announce that the fourth edition of the Office 365 for IT Pros eBook is now available. We have been working on this book for the last three months and it is great to see everything come together. You can’t simply announce a new edition…
-

Why You Should Come to Office 365 Engage…
As some of you know, I am the conference chair for Office 365 Engage, a new conference that emphasizes the need to treat Office 365 as a whole rather than a loose collection of mildy-cloudified on-premises applications. The event takes place in Haarlem, a rather nice town in the Netherlands,…
-
Analyzing the Office Servers and Services MVP community 2017
The MVP program (Microsoft Most Valuable Professional) is designed to recognize “technology experts who passionately share their knowledge with the community.” People are always curious about the make-up of the MVP group (including MVPs themselves), so I decided to take a closer look at the section to which I belong.…
-
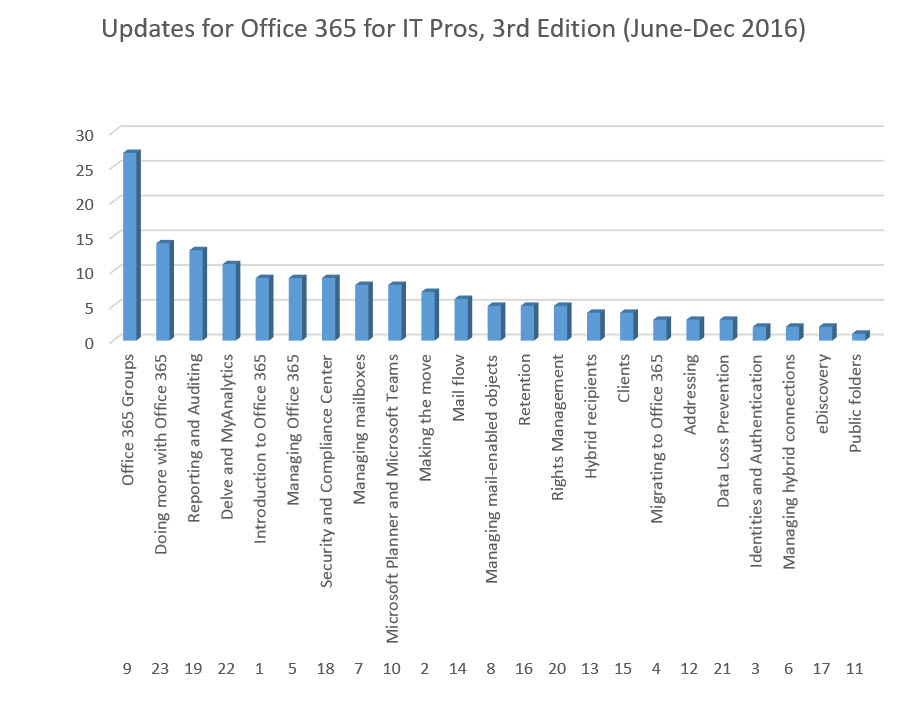
Analyzing Updates for the Office 365 for IT Pros eBook Since June 2016
The Office 365 for IT Pros eBook has been extensively updated since its initial publication on June 1, 2016. This analysis shows the hot spots for change inside Office 365.
-
Subscribe
Subscribed
Already have a WordPress.com account? Log in now.
